Advertisement
Discuss the latest trends, threats, and solutions in the field of cybersecurity.
Advertisement
Advertisement
Cybersecurity is an ever-evolving field that aims to protect computer systems, networks, and sensitive information from unauthorized access, theft, and damage. As technology advances, so do the methods that cybercriminals use to breach security systems. In this blog, we will discuss some of the latest trends, threats, and solutions in the field of cybersecurity.
Trends in Cybersecurity:
Cloud Security: Cloud computing has gained immense popularity in recent years, and with the increase in cloud adoption, the demand for cloud security has also increased. Cloud security includes various measures like access control, data encryption, and authentication, to name a few. The trend of hybrid cloud solutions is also emerging, which combines both public and private cloud infrastructure.
Artificial Intelligence (AI) and Machine Learning (ML): AI and ML have significant potential in cybersecurity, as they can help in detecting and respond to cyber threats much faster than humans. ML algorithms can analyze large datasets to identify patterns that indicate potential threats, while AI-based security systems can learn from previous attacks and improve their threat detection capabilities.
Zero Trust: The concept of zero trust security is becoming increasingly popular in the cybersecurity industry. It assumes that no user or device can be trusted, and access to resources is only granted based on strict policies and verification processes. This approach is beneficial in preventing insider threats and data breaches.
DevSecOps: DevSecOps is an approach that integrates security into the software development process. This approach ensures that security is considered from the start of the development process, rather than as an afterthought.
Internet of Things (IoT) Security: With the growing popularity of IoT devices, it has become essential to ensure their security. IoT devices are often vulnerable to attacks, and securing them requires a combination of hardware and software measures.
Blockchain Security: Blockchain technology has gained popularity in recent years, and it has the potential to provide secure and transparent data storage. However, securing blockchain technology requires a combination of cryptography, consensus algorithms, and other security measures.
Threats in Cybersecurity:
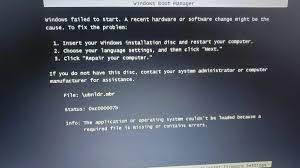
Ransomware Attacks: Ransomware attacks continue to be a significant threat to businesses and organizations. In these attacks, cybercriminals encrypt the victim's files and demand a ransom in exchange for the decryption key. In some cases, cybercriminals threaten to publish sensitive information if the ransom is not paid.
Phishing Attacks: Phishing attacks are a form of social engineering where cybercriminals trick individuals into revealing sensitive information such as login credentials, credit card details, or other personal information. These attacks are usually carried out through email, phone calls, or text messages.
Insider Threats: Insider threats are often the most significant threat to an organization's cybersecurity. These threats can come from current or former employees who have access to sensitive data and can intentionally or unintentionally misuse it.
Solutions in Cybersecurity:
Multi-factor Authentication (MFA): MFA is an essential security measure that requires users to provide multiple forms of identification to access resources. This approach provides an additional layer of security and reduces the risk of unauthorized access.
Security Information and Event Management (SIEM): SIEM is a security solution that collects and analyzes security-related data from various sources in real time. This approach enables organizations to detect and respond to potential threats more effectively.
Endpoint Protection: Endpoint protection solutions are designed to protect endpoints, such as laptops, mobile devices, and servers, from cyber threats. These solutions include anti-virus software, firewalls, and intrusion detection systems.
Advanced Persistent Threats (APTs): APTs are sophisticated and long-term attacks that are designed to remain undetected for an extended period. These attacks often involve multiple stages, and they can be challenging to detect and prevent.
Supply Chain Attacks: Supply chain attacks involve targeting an organization's third-party suppliers or vendors to gain access to the organization's network. These attacks are challenging to detect and can be highly damaging.
Fileless Malware: Fileless malware attacks are becoming more common, and they involve using legitimate system tools to execute malicious code. This approach can evade traditional anti-virus software and other security measures.
In conclusion, cybersecurity is a critical aspect of modern society, and it requires constant attention and innovation to keep pace with emerging threats and trends. The solutions mentioned above are just a few of the many tools and techniques that can be used to protect against cyber threats. It is essential to stay up to date with the latest developments in cybersecurity and implement a comprehensive security strategy to safeguard against cyber attacks.
Advertisement